On a Friday in early March, nearly 1,000 people queued outside Tencent’s Shenzhen headquarters just to get OpenClaw installed on their laptops. Within days, “raising a lobster” – China’s nickname for tending an AI agent – went from niche meme to national obsession.
The hype is real. People are lining up for OpenClaw installs in China. Even my grandma asked me to install OpenClaw for her.
— Crystal (@crystalsssup) March 9, 2026
but I still can't figure out why the hype started 😂 https://t.co/Ukd9k5KXip pic.twitter.com/I7b47qzlVc
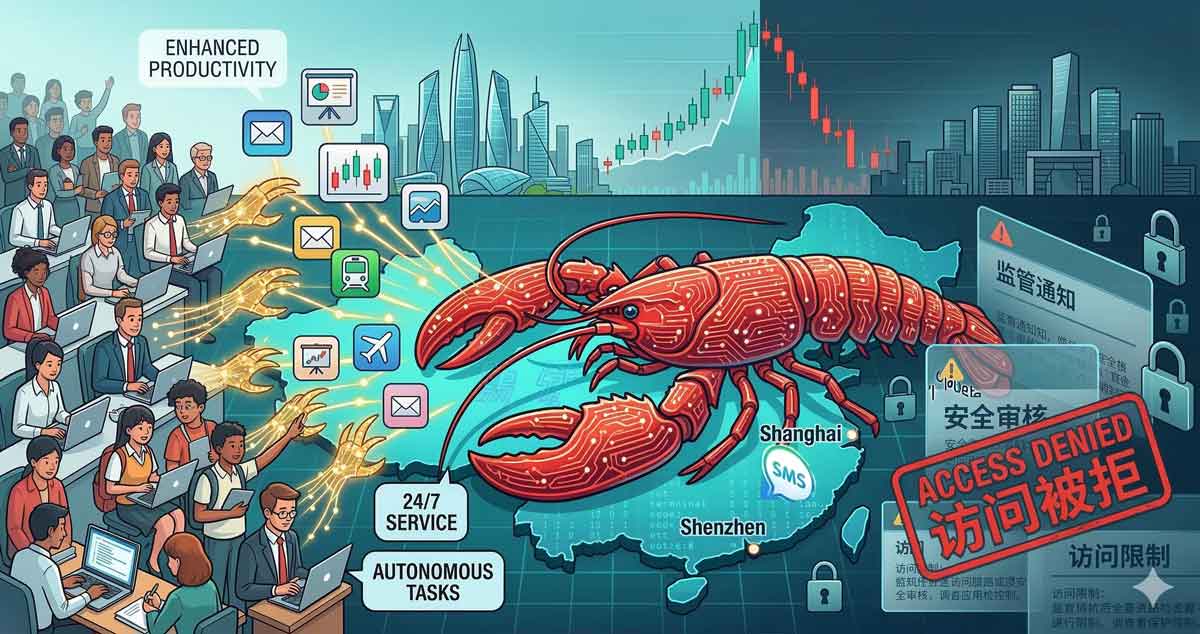
For a brief window, OpenClaw seemed to promise virtual staff for everyone: drafting reports, building slide decks, replying to emails, even trading stocks while you slept. Yet behind the memes and subsidies, security teams and regulators were already warning that this new “lobster” could claw straight through corporate perimeters and personal privacy.
This article traces China’s OpenClaw journey – from discovery to hyper‑adoption, then to tightening rules and growing backlash – and explores why the country can move from the world’s fastest laboratory to the world’s hardest brake on disruptive AI agents. By the end, you’ll have a timeline, a framework to understand China’s policy whiplash, and a practical takeaway for anyone building agentic AI in markets like Hong Kong, Shenzhen, or Singapore.
The OpenClaw Timeline: From Discovery to Frenzy
Late 2025 – Quiet Discovery, Cheap Intelligence
OpenClaw launched globally in late 2025 as an open‑source agent capable of running chains of tasks on top of large language models. Chinese developers quickly noticed its flexibility and its ability to plug into local models from Moonshot AI and MiniMax at lower cost than US‑centric alternatives.[9]
By February 2, 2026, OpenClaw was already described as a runaway success, explicitly positioning itself around “value for money” by adopting Chinese foundation models such as Kimi K2.5 and MiniMax’s agents. This “good‑enough plus cheap” positioning mattered in a market where cloud budgets are scrutinised and AI ROI is expected fast.

Hyper‑Adoption: Lobster Fever Takes Over
Early March 2026 – Queues, Side Hustles, and One‑Person Firms
On March 7, SCMP documented how OpenClaw suddenly broke out of developer circles into the mainstream. In Shenzhen, close to 1,000 people lined up at Tencent’s campus for free installation, spanning amateur coders, retired space engineers, housewives, and students.
As the AI assistant #OpenClaw surges in popularity in #China, paid installation services are popping up on social media. Some offer remote setup for 300 yuan (US$40) or in-person service for 500 yuan (US$70), while one user claimed to have made 260,000 yuan (US$36,000) in just a… pic.twitter.com/CQBDj5Jx2N
— Shanghai Daily (@shanghaidaily) March 6, 2026
Across Chinese social platforms, posts offering OpenClaw installation services – priced from tens to hundreds of yuan – turned into a micro‑economy overnight. Checks by regional media found listings on Xianyu and Xiaohongshu for remote and in‑home support, alongside a wave of “one‑person firms” using OpenClaw to automate client work, from slide building to basic coding.
Tech Giants Turn OpenClaw into Infrastructure
Chinese internet majors rapidly converted the hype into productised access.
- Tencent launched QClaw, plugging OpenClaw into WeChat so users could remotely control their laptops via chat commands after a three‑minute install.
- Alibaba published integration guides for DingTalk with unlimited OpenClaw API calls through March 31 and tutorials for deploying it on Alibaba Cloud from just 9.9 yuan.
- ByteDance’s Volcano Engine released ArkClaw, an “out‑of‑the‑box” cloud‑hosted OpenClaw variant that removed local configuration friction.
Local governments joined the party: Shenzhen’s Longgang district drafted subsidies up to 2 million yuan per OpenClaw project, while Wuxi’s hi‑tech zone offered 1–5 million yuan to accelerate industrial applications like quality inspection and predictive maintenance.
These moves turned a single open‑source agent into a de facto national platform – one that sat inside corporate networks, on personal devices, and deep in cloud environments in a matter of weeks.
Hyper‑Regulation: From Warnings to Dos and Don’ts
Mid‑March 2026 – Security Agencies Hit the Brakes
Even as local authorities subsidised deployments, China’s cybersecurity community sounded alarms. The National Computer Network Emergency Response Technical Team (CNCERT) issued its second formal warning about OpenClaw on March 11, highlighting severe security and data risks from improper installation.
CNCERT emphasised that OpenClaw’s autonomy demands high‑level permissions, which creates fertile ground for prompt injection, browser hijacking, and destructive misfires.
In one scenario, malicious web content could quietly instruct an agent to leak system keys; in another, a misinterpreted user command could trigger mass deletion of emails and critical files.
MIIT’s “Six Dos and Six Don’ts”
China’s Ministry of Industry and Information Technology (MIIT), via the National Vulnerability DataBase, followed up with prescriptive safety rules: six “dos” and six “don’ts” for OpenClaw deployment.
Key “dos” included:
- Use only the official, latest version of OpenClaw.
- Minimise internet exposure and grant minimum necessary permissions.
- Treat third‑party skill markets with caution and regularly patch vulnerabilities.
Key “don’ts” included:
- Don’t run outdated or mirror builds.
- Don’t expose agent instances directly to the internet or use admin accounts by default.
- Don’t install skill packs that request passwords or browse unverified websites; don’t disable detailed log auditing.
In parallel, Hong Kong tech stocks dipped as investors priced in the likelihood that Beijing would curb the OpenClaw frenzy – a reminder that China’s regulatory signals can reprice markets almost as quickly as they reprice technology risk.
Hyper‑Rejection: When a Lobster Bites Back
China has not formally banned OpenClaw as of mid‑March 2026, but the narrative has visibly pivoted from celebration toward risk containment. What began as “lobster fever” is now framed through security, compliance, and systemic risk, especially for critical infrastructure and large enterprises.
Several dynamics are driving this emerging rejection phase:
- Attack surface shock – Once agents are wired into messaging apps, file systems, and browsers, security teams realise they have effectively introduced a semi‑autonomous super‑user into every endpoint.
- Governance mismatch – Corporate and government IT controls were designed for static apps and human workflows, not self‑updating agents that can chain actions based on LLM outputs.
- Political risk – In a year when AI‑driven productivity is politically encouraged, any widely reported incident – say, a local government breach via OpenClaw – could trigger a swift clampdown to signal control and stability.
As Chinese local media begin to highlight removal services alongside installation services, you can already see the pendulum swing: there is money to be made in both raising and “culling” lobsters. Hyper‑rejection in China rarely looks like a single ban notice; it looks like a dense web of safety rules, liability fears, and informal pressure that make a once‑default choice suddenly feel radioactive.
Why China Moves From Hype to Hard Stop So Fast
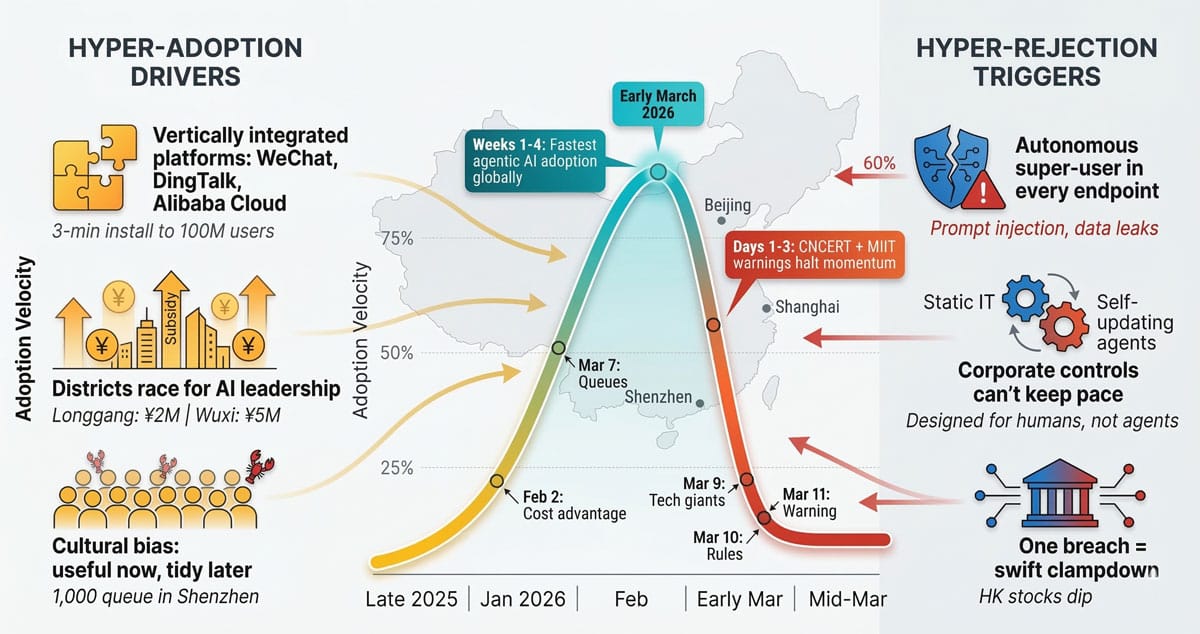
Structural Drivers: Integration, Local Incentives, and Policy Speed
China’s OpenClaw story is not an anomaly; it is how the system handles most disruptive technologies. Several structural features explain the whiplash.
- Vertically integrated tech stacks
Chinese cloud providers, super‑apps, and enterprise platforms can wire a new tool like OpenClaw into payments, messaging, and SaaS with minimal friction. The same integration that accelerates adoption magnifies blast radius when something breaks. - Local government competition
Districts such as Longgang in Shenzhen and the Wuxi hi‑tech zone race to signal alignment with Beijing’s AI priorities, offering subsidies that push rapid experimentation before governance is fully in place. - Central policy choreography
At national events like the Two Sessions, policymakers elevate AI agents as a key lever for a new “smart economy”, which encourages aggressive rollout. But the same apparatus can quickly issue risk advisories, technical guidelines, and targeted enforcement that chill adoption in sensitive sectors.
Cultural and Market Expectations: Hyper‑Effectiveness as a Feature
There is also a cultural and market expectation in mainland China that when a technology is useful, it should be scaled now and tidied up later.
Consumers in places like Shenzhen and Beijing are used to being early adopters, and enterprises expect AI tools to deliver tangible labour savings – such as treating OpenClaw as “virtual staff” – within weeks, not quarters. As a result, marginal tools rarely gain traction, but those that cross the usefulness threshold can reach national scale in a month.
The flip side is equally stark: once a technology is perceived as a systemic risk – whether for data, social stability, or international optics – there is little tolerance for slow, negotiated rollbacks. Hyper‑adoption and hyper‑rejection are two sides of the same optimisation mindset.
Takeaways: Designing for China’s Hyper‑Efficient Disruption Cycle
China’s OpenClaw saga underscores a broader truth: when it comes to socially disruptive technologies, the country is both the fastest experimental lab and one of the strictest long‑term gatekeepers. For builders and executives in Hong Kong, Shenzhen, Singapore, or Ho Chi Minh City, that has three practical implications:
- Assume adoption velocity will exceed your governance maturity. If you plug agentic AI into core workflows, design for rollback from day one – kill‑switches, permission tiers, and human‑in‑the‑loop checkpoints.
- Treat regulators as design partners, not post‑hoc reviewers. MIIT’s dos and don’ts read like a security product spec; anticipate similar requirements in your own markets and bake them into reference architectures.
- Optimise for controllable usefulness, not maximal autonomy. In environments primed for hyper‑reaction, the safest growth path is to make your agent indispensable without making it uncontrollable.